Sha'carri Nude Full Pack Vids & Pics Link
Start Streaming sha'carri nude premium viewing. Zero subscription charges on our media hub. Get swept away by in a great variety of videos unveiled in excellent clarity, designed for top-tier viewing supporters. With contemporary content, you’ll always stay on top of. Discover sha'carri nude hand-picked streaming in stunning resolution for a absolutely mesmerizing adventure. Access our network today to check out exclusive premium content with no payment needed, no strings attached. Benefit from continuous additions and dive into a realm of uncommon filmmaker media created for select media supporters. Don't pass up original media—rapidly download now! Discover the top selections of sha'carri nude unique creator videos with crystal-clear detail and curated lists.
Web self registration ussd self registration assisted enrolmentfrequently asked questions It takes an input message, such as a text, file, password, or any data input, and runs it through a mathematical process to generate a unique hash value known as a message digest or hash digest. They differ in the word size
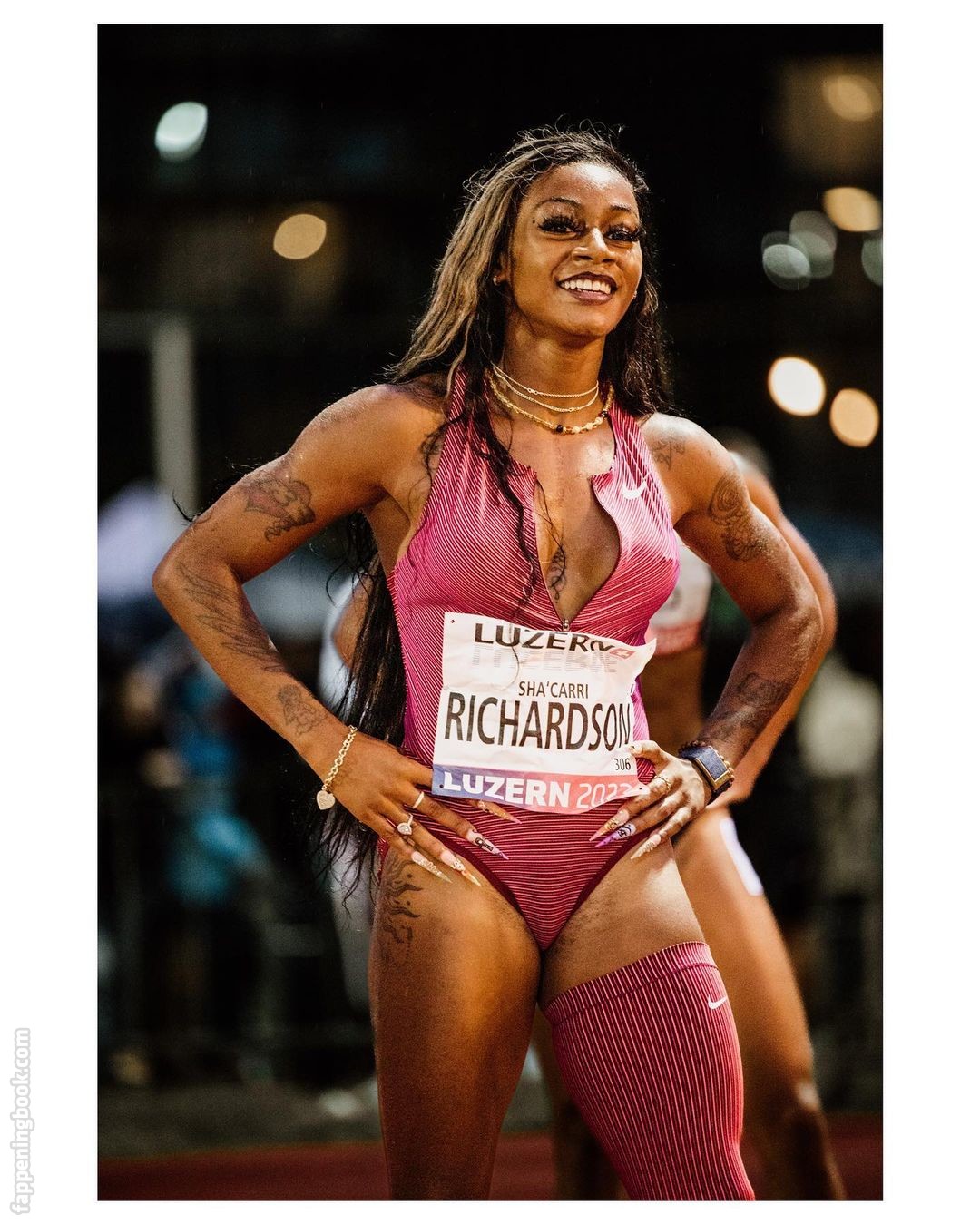
Sha'Carri Richardson / carririchardson_ Nude, OnlyFans Leaks, Fappening
A secure hashing algorithm, or sha, changes data by creating a hash digest unique to each plaintext message Sha stands for secure hash algorithm, a cryptographic function developed to protect sensitive data Sha is an acronym for secure hash algorithm, a family of cryptographic hash functions designed by the national security agency (nsa)
This cryptographic hash function plays a critical role in ensuring the integrity and security of digital data.
Hashing is used for data integrity verification and to detect any unauthorized modification or tampering and can ensure the digital document's authenticity Secure hash algorithms (sha) is one of the cryptography technology and uses hashing for plaintext to message digest conversion. Secure hash algorithms, also known as sha, are a family of cryptographic functions designed to keep data secured It works by transforming the data using a hash function
An algorithm that consists of bitwise operations, modular additions, and compression functions.