Iam_eli Leaked 2026 Archive Media Files Full Link
Activate Now iam_eli leaked world-class media consumption. No recurring charges on our on-demand platform. Delve into in a immense catalog of media presented in crystal-clear picture, suited for superior streaming followers. With trending videos, you’ll always stay current. Check out iam_eli leaked expertly chosen streaming in retina quality for a mind-blowing spectacle. Hop on board our content portal today to enjoy exclusive premium content with with zero cost, no subscription required. Receive consistent updates and journey through a landscape of bespoke user media tailored for select media buffs. Be sure to check out uncommon recordings—click for instant download! Witness the ultimate iam_eli leaked rare creative works with sharp focus and curated lists.
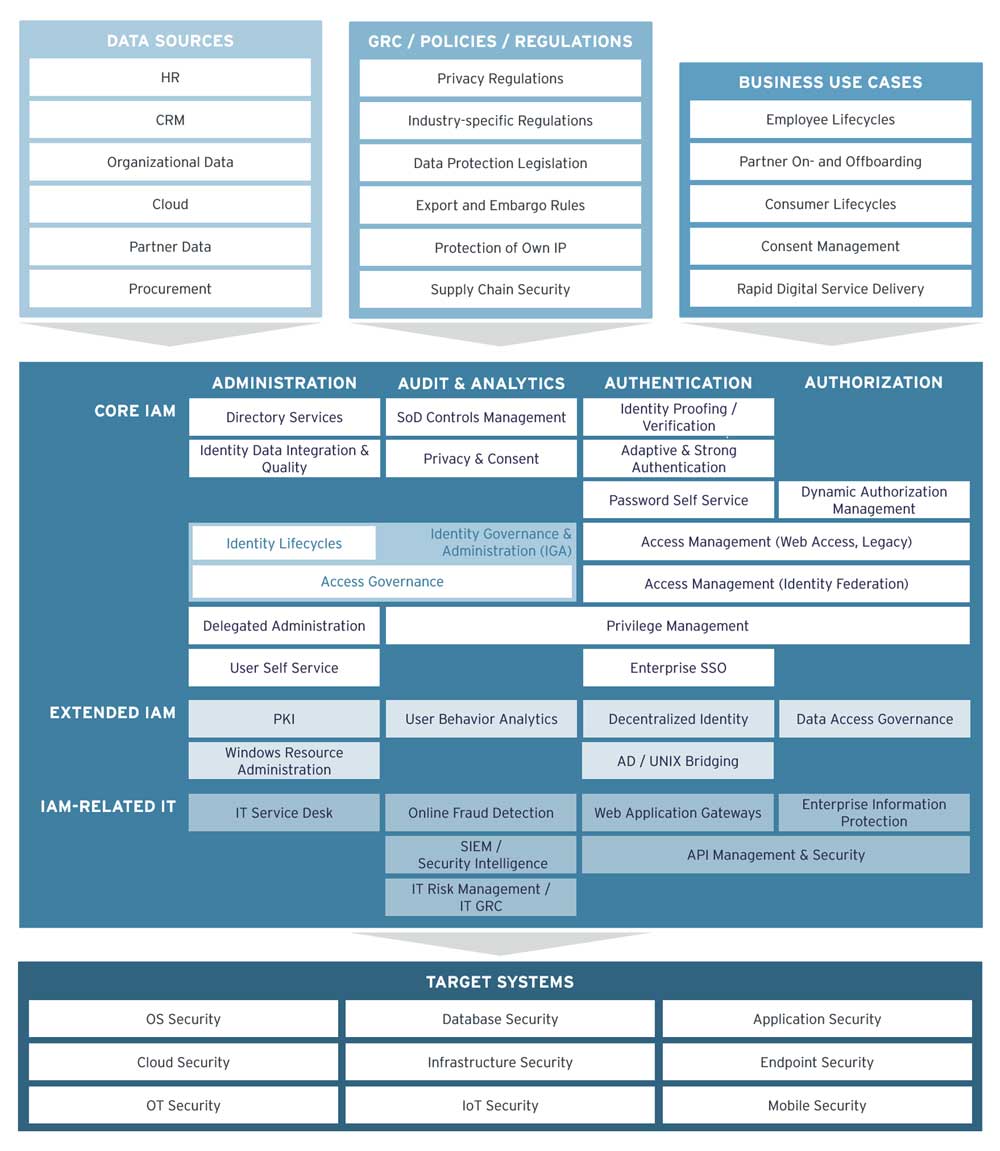
Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities. Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity. With nearly 600,000 active and retired members, the iam is one of the largest and most diverse labor unions in north america
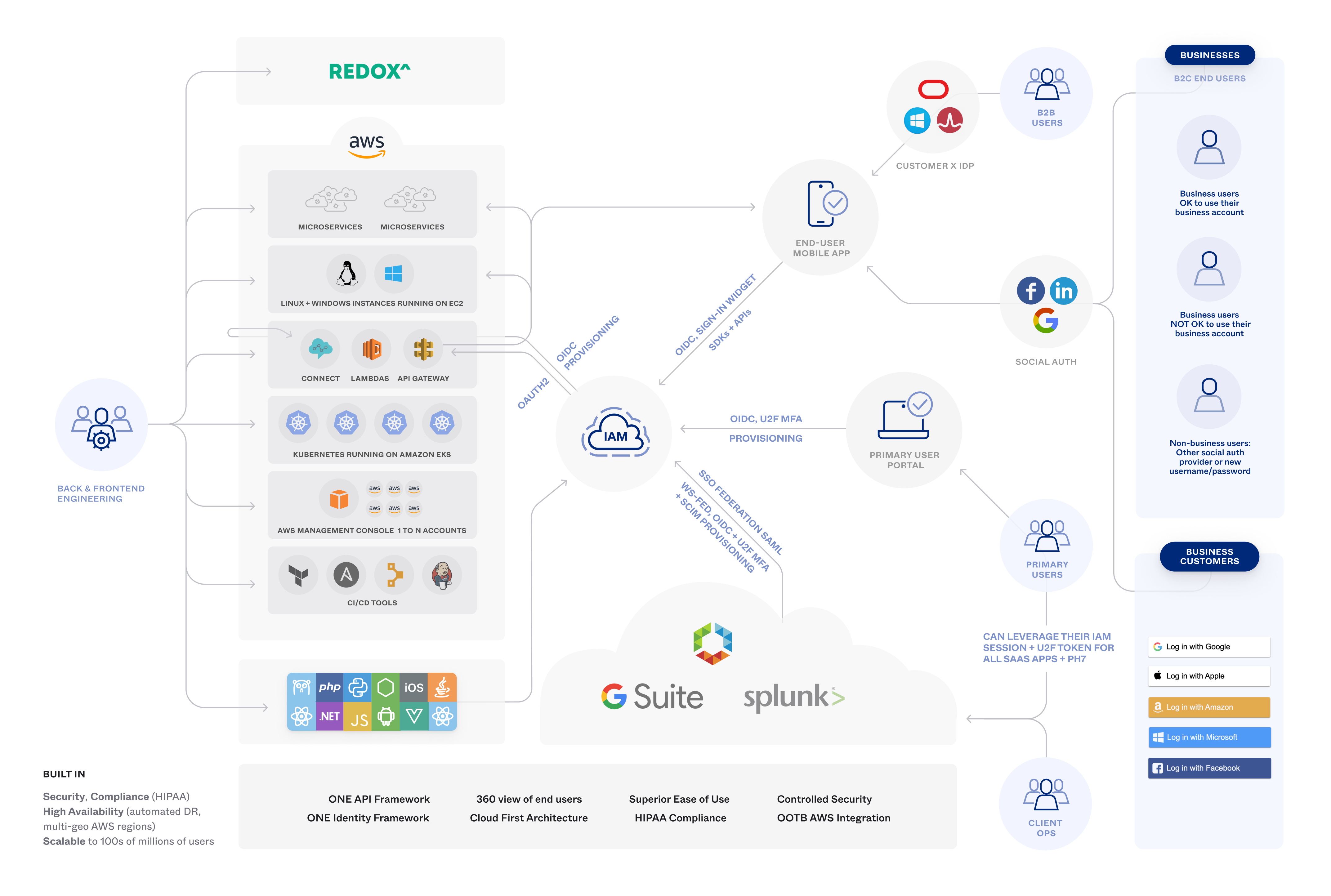
Onelogin Workforcecustomer Identity Access Management
Learn about aws identity and access management (iam), its features, and basic concepts. We currently serve over 40,000 active and retired members at 44 locals across the united states, including alaska, hawaii and puerto rico Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms.
Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information.
Identity and access management is a fundamental and critical cybersecurity capability Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time. Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system Iam tools help ensure that the right people can access the right resources for the right reasons at the right time.
Learn the core concepts of identity and access management (iam), including authentication, authorization, and identity providers, to secure resources effectively.